Archive
DH2i CEO Don Boxley announces a new DxEnterprise (Podcast)
 DH2i CEO and co-founder Don Boxley and I had a good discussion about the new version (v17) of DxEnterprise. Don explains that this major upgrade is something you’ll want if you’re a current DxEnterprise user and something you want to consider if you’re not. DxEnterprise is a multi-platform, smart availability platform for your virtual machines. If you want to know what smart availability is and all of version 17’s new enterprise features are, listen to the podcast. Technical folks will love the new platform and its extreme availability features. I have to say that I’m impressed and if you know me, you know that’s not an easy thing to do.
DH2i CEO and co-founder Don Boxley and I had a good discussion about the new version (v17) of DxEnterprise. Don explains that this major upgrade is something you’ll want if you’re a current DxEnterprise user and something you want to consider if you’re not. DxEnterprise is a multi-platform, smart availability platform for your virtual machines. If you want to know what smart availability is and all of version 17’s new enterprise features are, listen to the podcast. Technical folks will love the new platform and its extreme availability features. I have to say that I’m impressed and if you know me, you know that’s not an easy thing to do.
 The new version gives you Linux, Windows, and Docker smart availability with reduced complexity. Business continuity, as we say in the podcast, is an essential feature of any service these days and that’s exactly what you’ll get with DxEnterprise v.17.
The new version gives you Linux, Windows, and Docker smart availability with reduced complexity. Business continuity, as we say in the podcast, is an essential feature of any service these days and that’s exactly what you’ll get with DxEnterprise v.17.
From a system administrator point-of-view, I can live with less complexity, more uptime, greater flexibility, and broader support for my enterprise systems.
Podcast details:
Length: 32:45 mins. Format: MP3. Rating: G for all audiences.
Thanks and apologies to both Don and Nicole for being very flexible and accommodating for this interview and subsequent posting.
Atlantis Computing’s Software Defined Storage, Hyperconverged Infrastructure, and Data Center Design
 Atlantis Computing‘s Hyperscale appliance sports an all-flash array for storage, plus adds compute and virtualization to your remote office/branch office (ROBO) sites without the need for on-site IT staff. Its Hyperscale solutions offer your company:
Atlantis Computing‘s Hyperscale appliance sports an all-flash array for storage, plus adds compute and virtualization to your remote office/branch office (ROBO) sites without the need for on-site IT staff. Its Hyperscale solutions offer your company:
- Data reduction
- I/O acceleration
- Data management
- Data mobility
- Data protection
- Unified storage
Its “turnkey” appliances offer simplified setup with enterprise-class all-flash storage that anyone in your ROBO can setup in minutes at a lower cost than competitive hyperconverged solutions. Starting with a two-node, 4 TB appliance, your Atlantis Computing-based solution can grow with you. You can read my article on ZDNet about Atlantis Computing’s latest announcements and listen to the podcast.
To find out more about how Atlantis Computing’s Hyperscale solutions can help your business, check out an in-depth article complete with supporting statistics and data: From the Field: Software Defined Storage and Hyperconverged Infrastructure in 2016.
Atlantis Computing is also offering you a free ebook so that you can have a look into the building of a modern data center.
Learn how agile IT principles and emerging data center services, such as software-defined storage and a hyperconverged infrastructure, will play an important role in meeting increasing business demands.
Sign up to reserve your copy.
Other free resources from Atlantis Computing:
DeepStorage Report on Atlantis
Atlantis Computing also helps companies setup and manage virtual desktop infrastructure (VDI) implementations. If you want your VDI to work like you’ve dreamed it would without spending your company’s retirement fund to do it, check out Atlantis’ solutions for VDI.
Disclaimer: This is a non-sponsored post.
Sponsorship: If you would like to sponsor a post or have me review a product, contact me via Twitter @kenhess.
The Sixth Flag Launches a Highly Secure Desktop As A Service for the Enterprise
Raleigh, N.C. – March 25, 2015 – The Sixth Flag, Inc. (TSF), an emerging new technology firm, today released its web-based, HTML-rendered Desktop-as-a-Service that requires no dedicated hardware. The offering provides a unique solution specifically designed to address the increasing challenges faced by today’s distributed workforce. With nothing more than a browser, users can access their cloud-based corporate desktop, whether from a laptop, PC desktop or tablet. Because user data is not stored on the local device, loss of a device does not represent compromised sensitive company data.
According to Pete Kofod, co-founder and CEO at TSF, “Our solution targets mobile users, contract, seasonal and temporary personnel as well as select employees that are targeted for corporate espionage.”
“Taken together, those groups of corporate technology users consume disproportionate resources to prevent security breaches and mitigate data risk. When you include the compliance requirements and capital costs associated with asset management, organizations of all sizes face serious challenges when dealing with the complexities of managing the desktops of a globally distributed work force.”
“The prevailing ‘solutions’ today are limited to one-offs,” Kofod explains. “Corporate technology departments need to be flexible in resource allocation, yet a significant part of the overall budget is the capital outlay towards corporate desktops, forcing IT staff to continuously support one-off solutions for these emerging requirements, which are neither practical nor cost effective.”
Unlike other vendors offering Desktop-as-a-Service solutions, The Sixth Flag is specifically designed to serve the remote enterprise user. “What we do is pretty straight forward,” Kofod continues. “we offer secure, easy-to-manage desktops to remote users without breaking the bank.”
According to David Kinghorn, co-founder and chief technology officer, by using TSF’s solution, organizations can manage the configuration and software installed on the desktop, including popular office productivity and line of business applications. TSF supports a complete Microsoft-based desktop user experience, including print and file management and more.
“With our offering, all you need is a current web browser,” he says. “This includes all desktops as well as tablets, because we do not rely on any plugin or download.”
At the end of every computing session, all user information is encrypted, stored and the desktop is, in effect, destroyed. Subsequently, every time a user logs in, they receive a fresh desktop with their data and settings intact. Kinghorn points out that any persistent threat that has found its way on to the desktop is deleted along with the desktop at the session’s end.
Exclusive to the TSF offering is a patent-pending “watermark” function. The unique pattern is overlaid on the screen session, discouraging users from leaking sensitive data by photographing or capturing desktop screen shots. “We received requests for this feature from firms that have been significantly harmed by unauthorized leaks,” says Kofod.
TSF supports Active Directory authentication. System administrators can implement traditional desktop group policies. Additionally, the administrators can also restrict uploads/downloads, Internet access, printing, copy and paste, as well as other functions using the TSF administrative console.
In its most restrictive configuration, TSF is comparable to a “clean room” in biotech. What happens on that desktop cannot leave. It can’t be sent via email or saved to cloud-based file storage.
“When high-risk groups collaborate using The Sixth Flag, they are in essence fenced off, without any meaningful drop-off in productivity,” he says. “Even if they pick up malware, it disappears when they sign off.”
No capital investment or long-term commitment is required. From service costs, to desktop licensing, TSF rolls all those costs into a monthly fee. For organizations that have seasonal, temporary or contract workers, there is no need to make a long term investment to meet short term requirements.
With today’s increasing demand for “bring your own device” (BYOD) working environments, IT departments face the challenge of maintaining internal controls through a standardized corporate platform. TSF enables full BYOD, eliminating the need to provide and manage end-user physical desktops, while facilitating standardization and significantly reducing capital expenditures on desktop hardware.
“Best of all,” Shane Yocum, Vice President of Business Development notes, “TSF can be deployed for an organization in as little as 20 minutes. A recent use case is a customer wanting to set up a disaster recovery environment. There is no way to do that cost effectively using traditional DaaS licensing,” he notes, “but we have a DR licensing model that allows organizations to maintain a Desktop DR environment very economically.”
About The Sixth Flag, Inc.
The Sixth Flag Inc, is a Raleigh, North Carolina-based Desktop-as-a-Service firm for global teams and organizations in need of Remote Desktop Management solutions. Launched in 2015, TSF provides a web-based, cost effective and secure throw away desktop for today’s global, mobile teams. Its cloud-based, HTML-rendered Desktop-as-a-Service requires no dedicated hardware, thereby eliminating the need for organizations to spend on capital outlay. With nothing more than a browser, users can access their corporate desktop from anywhere in the world, whether from a laptop, desktop, or tablet. Because user data is not stored on the local device, loss of a device does not represent compromise of sensitive organizational data. For more information, visit www.thesixthflag.com
Introducing the Microsoft Migration Accelerator for Azure
Announcing the limited preview of the Migration Accelerator (MA), for Azure. Spawned from the technology of Microsoft’s InMage acquisition announced July 11th the MA is designed to seamlessly migrate physical, VMware, AWS and Hyper-V workloads into Azure. It automates all aspects of migration including discovery of source workloads, remote agent installation, network adaptation and endpoint configuration. With MA, transitions into Azure can occur in mere minutes!
MA changes the cloud migration paradigm by offering:
- Heterogeneity: With MA you can migrate workloads running on a broad range of platforms such as VMware, Microsoft Hyper-V, Amazon Web Services and/or Physical servers within your environment. MA can support workloads running on Windows Server 2008 R2 sp1, Windows Server 2012 and Windows Server 2012 R2 operating systems.
- Simple, Automated Migration: The MA portal allows you to automatically discover your enterprise workloads, remotely from the cloud. With few clicks you can configure end-to-end migration scenarios. MA allows you to test your workload in the cloud without impacting the existing on premise production workload, offering the ability to validate workload functionality before a cutover is performed.
- Migrate Multi-tier Applications: MA boasts the unique ability to migrate multi-tier production system with application level consistency, orchestrated across tiers. This ensures multi-tier applications run the same in Azure, as they ran at the source. Application startup order is even honored, without the need for any manual configuration.
- Continuous Replication, Least Cutover Time: MA for Azure provides full-system replication including the OS and application data. This continuous replication and in-memory change tracking reduces the cutover time to mere minutes, minimizing impact to production workloads.
How MA works
MA uses multiple components to orchestrate your migration project as shown below:
- Mobility Service: A light weight (guest based) centrally deployed agent which gets installed on source servers (on-premises physical or virtual) to be migrated to the target virtual machines on Azure. It is responsible for real time data capture and synchronization of the selected volumes of source servers to target servers.
- Process Server (PS): A physical or virtual server that is installed on premise. It facilitates the communication between the Mobility Service and target virtual machines in Azure. It provides caching, queuing, compression, encryption and bandwidth management.
- Master Target (MT): A target for replicating disks of on premises servers. It is installed within a dedicated Azure VM in your Azure subscription. Disks are attached to the MT to maintain duplicate copies.
- Configuration Server (CS): Manages the communication between the Master Target and the MA Portal. It is installed on a dedicated Azure VM in your Azure subscription. Regular synchronization occurs between the CS and MA Portal.
- MA Portal: It is a multitenant portal by which you can discover, configure protection and migrate your on premise workloads into Azure.
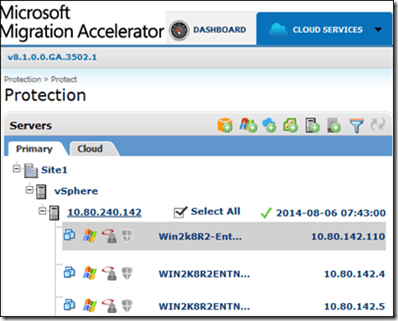
MA automates all critical processes required to migrate a source workload within an Enterprise into Azure Cloud. It can discover on premise workloads running in ESX/Hyper-V, AWS or physical servers. The workloads are discovered using a Process Server which is connected to MA portal. The discovered instances are listed in MA portal as shown below:
You can choose particular instance(s) from the discovered list of workload for migration. The next step is to install the Mobility Service (agent) on the source servers. This can be remotely orchestrated from the MA portal by choosing ‘Install Mobility Service’ option as shown below:
After installing the Mobility Service, you can configure replication for selected servers by choosing the Protect option. MA uses the configuration details garnered from the discovery process for the protected source servers to determine and provision the most suitable sizing for the environment within Azure. In addition, the target VHDs are provisioned on the Master Target. Once replication is setup, synchronization of the on premise server disk to the target VHD in the Azure cloud begins.
Now, that you have configured the initial sync, wait to ensure the initial replication is complete. After initial replication, select the Migration option from the Cloud Services menu.
From the list of protected servers that appear under Protected Application, select the “protection plan” or list of assets you wish to migrate.
Once you choose a protection plan it will appear under Migration > Selected Hosts. Click Migrate to start the migration process.
You can now monitor the progress of migration under Migration Scenarios > Migration Status.
After successful migration, Virtual Machines are created in Azure Cloud. You can now logon to the migrated VMs to validate if the running instances on the cloud is identical to your source.
Summary
In summary, MA offers an unprecedented level of automation to provide seamless migrations of heterogeneous assets, into Azure.
Key Highlights:
- Automated asset discovery and migration – MA portal orchestrates the discovery and migration of workloads from a single pane of glass.
- Migration cutovers to Azure in minutes – continuous replication and in-memory change tracking significantly reduce cutover time.
- Self-provisioned target Azure VM’s – Target VMs are dormant during synchronization saving compute cost and are then automatically provisioned during cutover.
- Heterogeneous platform support – support for broad range of environments and platforms.
- Continuous replication – lightweight agents on the source servers continuously replicate all changes to target ensuring near zero downtime during migrations.
- Multi-tier application support – migrate your multi-tier production system with application level consistency orchestrated across tiers.
- Target VM Network and Endpoint Adaptation – support for automated network adaptation and endpoint reconfiguration.
- Integrated compression, encryption and bandwidth management.
To get started visit Microsoft Migration Accelerator and sign-up for preview.
Ken Hess’ Topics of Interest
I am always looking for article ideas and topics from readers, companies, PR folks, friends, and techies. This page is where I post my current needs. I have a variety of venues for articles. I decide where I post the information according to interest, audience, and other factors.
If a topic is posted here, I’m interested in interviews, discussions, podcasts, infographics, ideas, and data related to it. Feel free to contact me via email (ken-at-kenhess-dot-com) or Twitter (@kenhess) to continue the dialog. Please read the complete list of needs and the list of things I’m not looking for.
CURRENT NEEDS:
Internet of Things & Machine to machine communications
- Users
- Use cases
- Case studies
- Infographics
- Statistics
- Perspectives
- Security
- Pain Points
- Successes
- Clever applications
Security
- Breaches, thefts, hacks
- Vulnerabilities
- Successes
- Costs and cost data
- Challenges
Virtualization
- Special virtualized workloads
- Interesting applications
- Challenges
- New frontiers
- Cloud applications
Consumerization/BYOD
- Solutions
- Challenges
- Success stories
- Pain points
- Productivity Apps
- Security
Big Data
- Case studies
- Statistics
- Users
- Alternatives
- Challenges
- Solutions
Offshore outsourcing
- Failures
- Expose’
- Non-performance issues
- Challenges
- Cost vs. return
- Scams, deals gone wrong, security problems
Technical Startup Companies
- Profiles
- Innovations
- Technology overview
- David and Goliath stories
- Successes
NOT CURRENTLY LOOKING FOR:
Funding information
Partnerships/Strategic Partnerships
Healthcare-related
Fashion-related
Food-related
Mid-market Business Cloud Transition Pain Points (Podcast)
IBM’s Vice President of Global Mid-market Sales, Mike McClurg, and I discuss IBM’s role in transitioning mid-sized businesses into virtualized infrastructures and cloud-based technologies. We discuss IaaS, SaaS and pain points associated with the shift to hosted solutions. 21 minutes. MP3 format.
IBM_MidMarket_Cloud_Discussion_with_MikeMcClurg_Apr_2012
This post was written as part of the IBM for Midsize Business program, which provides midsize businesses with the tools, expertise and solutions they need to become engines of a smarter planet.
Has the World outgrown Commercial UNIX?
When you read articles about cloud computing or Enterprise computing, you rarely see the term ‘UNIX’ anymore. You see plenty of rhetoric about Linux and Windows but UNIX seems to have left the building, for good. And, by ‘building,’ I mean data center. However, that’s not the case. UNIX is alive and well in the world’s Enterprise data centers. It just doesn’t grab headlines like it used to. Does the fact that UNIX isn’t a newsworthy buzz term mean that it’s on its last legs as an Enterprise operating system. Certainly not. Commercial UNIX might have lost its “coolness” but it hasn’t lost its place running your business-critical applications and services.
Enterprise-level UNIX systems still rule the data center for the big workloads, the big databases and Big Data.
When selecting an operating system for your critical business needs, what do you look for? Reliability, availability, stability, versatility, virtualization, scalability, affordability, sustainability, supportability and sheer ability are terms that come to mind on which to judge an operating system. Plus you need a company behind the operating system that employs experts who understand the critical nature of your business. That’s the lure of commercial UNIX. That’s the decision point for many businesses: Support.
It’s fun to think of living in a world where a company can throw caution to the wind and use free software. The reality is that for a company to remain operational it must do so sometimes at greater expense. It’s wise to be frugal but you also can’t afford to gamble with your business’s livelihood based on whim or attitude founded on an ideal. Free software has its place in the data center. But, are you willing to risk your company’s mission-critical business on it?
So far, businesses say, “No.”
Commercial UNIX still wins in every category listed above. Yes, even affordability. Companies that use Linux never do so without also paying for support and 24x7x365 is expensive, even for Linux. Windows does some things well. Linux does some things well. Commercial UNIX does some things well. There is no single right answer to every problem. That’s why you don’t have many companies of any size that have a single operating system or platform anymore.
Don’t misunderstand me, I love Linux and free software but you have to realize that, when it comes to risking millions or perhaps even billions of dollars on your computing infrastructure, you have to use a time-tested, battle-proven technology. That technology is commercial UNIX.
Allow me to quote some statistics gathered by Gabriel Consulting Group (GCG) last year (2011) on this topic that’s published in their whitepaper, “Is Commercial Unix Relevant in the Midmarket?” The 300+ survey respondents represent companies of all sizes, including 44 percent from companies with more than 10,000 employees. However, the data in the report reflects the responses from the focus group (Midmarket, 4,000 or fewer employees), which is 46 percent of the total number of those surveyed. GCG has also included some data from the large company segment for comparison.
- >80% stated that UNIX usage is increasing.
- 49% said that 75% or more critical applications run on UNIX
- >75% report that >50% mission-critical applications run on UNIX
- Larger organizations state that 75% of their critical applications run on UNIX
- 90% said that UNIX is strategic to their business
- 98% of large company respondents stated that UNIX is strategic
What are the most important factors to those who choose commercial UNIX for their mission-critical workloads?
- Availability and Stability
- Operating System Quality
- Predictable Performance
- Vendor Support
- Raw performance, Speed, Scalability
What are the less important factors for those who’ve selected commercial UNIX?
- Easy Administration and Management
- Acquisition Price
- System Familiarity
- Virtualization Capability and Tools
These two lists say a great deal about commercial UNIX buying habits. One glaring point is that price is of less consequence than reliability. The top three reasons given are the reasons why commercial UNIX has many more years of life left in it for the applications and systems that are business mission-critical.
One point that’s a bit unclear in the survey is that of scalability. Sure, Linux and Windows are both scalable but only on PC hardware. And, that includes virtualization. PC hardware can’t compare to the “big iron” on which commercial UNIX runs. Of course, Linux (zLinux) does run on mainframe computers (z/OS) and that’s pretty big iron but most companies under the 4,000 employee levels don’t own a mainframe.
Although survey respondents said that raw performance, virtualization and scalability were not high on their most important aspects list, they’re still important. So is support. The people who write the checks still like to rely on companies that back their products. Companies have more confidence in commercial UNIX than they do in Linux, even when supported by primary vendors such as Red Hat or Novell. Although the Debian distribution is free of charge, companies would rather engage and pay for a real company’s support behind the product.
To drive home the point, the survey revealed that 41 percent of respondents feel that commercial UNIX support is superior to that of Linux vendor support at 30 percent. And, 47 percent believe that UNIX is more available and more reliable than Linux.
Most small to medium-sized businesses (SMBs), like most Enterprises, have a heterogeneous environment. They run their mission-critical applications and services on commercial UNIX and user-oriented services (File, Web, Intranet) on Windows and Linux. Almost three-quarters of those surveyed said they would use commercial UNIX well into the future. While commercial UNIX doesn’t have that “cool” factor that Linux does, commercial UNIX still owns the mission-critical market.

This post was written as part of the IBM for Midsize Business program, which provides midsize businesses with the tools, expertise and solutions they need to become engines of a smarter planet.
Why You Need Infrastructure as a Service (IaaS)
Infrastructure as a Service is that part of cloud computing that allows you to lease and manage computing infrastructure for your business needs. Computing infrastructure includes virtual machines (VMs), operating systems, middleware, runtime components, network, storage, data and applications. Cloud computing vendors provide the necessary underlying physical hardware (servers, network, storage) that they own and manage transparently in the background. The two worlds have little crossover. The cloud vendor and customer have a non-intrusive relationship with one another just as you currently do with your web hosting provider. They’re there when you need help but their direct involvement in your business is zero.
The cloud vendor also supplies you with a management interface in which you work with your infrastructure. You’re responsible for license management for your operating systems and software. You pay for compute resources per CPU, per hour, per gigabyte of bandwidth, per gigabyte of storage or a combination.
The Three Faces of IaaS
IaaS isn’t as simple as a single offering but the boundaries between types are well-drawn. First, you have the Private Cloud. Private IaaS is exactly what you think it is—a dedicated, private infrastructure. Think of your own data center setup as a Private Cloud IaaS. Of course, unless you have cloud infrastructure (virtualization, storage, extreme redundancy, etc.), it isn’t officially a cloud but you get the idea.
On the other end of the spectrum is the Public Cloud. A Public Cloud is a 100 percent hosted solution. You own no hardware. It is the Public Cloud that is the focus of this article.
If you combine the two cloud concepts, you have what’s known as a Hybrid Cloud. A Hybrid Cloud can be any percentage mixture of Private and Public infrastructures for your company. Most companies will evolve into this type of cloud from a traditional, private hardware infrastructure to a cloud-based one.
A Hybrid Cloud is the solution that cloud vendors recommend to their customers who’ve grown their own data centers and that are comfortable with that model. Mix your Private Cloud with the Public Cloud for a solid and complete solution for you and your customers. A Hybrid Cloud mixes the security and control of a traditional data center with hosted cloud infrastructure. Typically, companies will transition their disaster recovery efforts to the Public Cloud while retaining production operations in-house in a Private Cloud.
Industry experts view Hybrid Clouds as a transitional step to a full Private Cloud. They see this process as a stepwise migration. As leases and service contracts expire, companies will move their computing workloads from private data center architecture and Private Clouds to virtualized architecture in the Public Cloud.
Analysts predict that by the end of 2012, as many as 20% of businesses will exist completely in the Public Cloud.
Cost Savings But Not Where You Think
Cost tops the advantages of IaaS cloud computing. To purchase the same amount of physical computing power, to manage that computing power and to house that computing power costs many times more than bulk pricing from a cloud vendor. IaaS is basically hardware outsourcing. You don’t own the hardware. You don’t manage the hardware. You use the hardware but its care and feeding are not your problem.
Put whatever moniker on cloud computing’s IaaS that you want but it’s really no different than what you probably do now in your current data center. Unless you own your data center, pay its staff, maintain the facility and physically service your own hardware, then you’re already using hardware (infrastructure) as a service. The primary difference in a standard data center space lease and IaaS is that you don’t have to deal with any hardware.
IaaS frees you from purchasing or leasing hardware, having it shipped to the data center, paying someone to deploy it into a rack, paying for that rack space, managing the hardware throughout its life cycle and taking care of its disposal. That’s why traditional data center infrastructure management is expensive. You have to pay for the hardware, you have to pay for maintenance, you have to pay for management and you have to pay for the business services that required all of this expense in the first place.
On the other side of the argument, cloud opponents state that your TCO is no lower with IaaS than with traditional data center service. This might be true from a pure hardware point-of-view. After all, the IaaS vendor has to pay for the data center infrastructure and pass his costs on to you. However, the savings is in the form of labor costs.
Count the number of full-time employees (FTEs) you have on hand right now to manage your infrastructure. Now, count the number of FTEs you’ll require by not managing any hardware. Is there a significant difference between the two numbers? Add up the total cost of those FTEs who you won’t need anymore and multiply that number by three years (standard hardware lease length). That number is your savings.
Since your new virtual infrastructure comes with online management tools for creating new servers, installing operating systems, presenting storage and configuring network, you’ll need fewer FTEs to handle the job.
Lower Entry Barriers and Rapid Innovation
IaaS also lowers the financial and logistical barriers for startup businesses to enter the market and push their products and services to customers in a fraction of the standard timeframe. The IaaS model allows startups to start small and grow to any size on the pay-as-you-go plan. There’s not a huge outlay of capital on hardware and FTEs that traditionally built businesses have experienced.
Another advantage of IaaS is rapid innovation. For example, if you have an idea for a new service today, you could spin up a virtual test infrastructure for a few hundred dollars, test your service, demo your service and deploy a working business model in a matter of days instead of months. In a time when windows of opportunity are often very small, IaaS makes sense for who need a quick service build-out to show investors or potential customers.
Embrace the Elastic and Mobile Cloud
IaaS also makes your company mobile, elastic and global. You can manage your systems from anywhere, you can shrink and grow your computing infrastructure as needed and you can keep your global customers happy with zero downtime. And, since you’re not tied to a server room or data center, your office location is irrelevant. You can work from home and your employees can be spread across the globe.
Have you ever had to move systems, network and storage from one location to another? If you have, you know about expense, outage and failure. Most cloud vendors maintain geographically disparate data center locations to ensure zero downtime for your infrastructure. Sure, there’s an additional cost for the service but how much is your current disaster recovery solution costing you?
Summary
You need IaaS because you need mobility, agility, stability, availability, elasticity and frugality in your business. You can save money. You can beat the competition to market. And, you can do it with the peace of mind that someone else is minding the hardware foundation under your business.
Where to Go from Here
If you’re considering moving to an IaaS solution or you’re part of a startup, contact a cloud vendor and discuss your needs. Remember that not all cloud vendors can or will give you good advice. Look for experience, longevity, availability, customer service and customer satisfaction in your quest to migrate to the cloud. Remember that your partnership with a cloud vendor is an important one. It’s more than a simple landlord-tenant relationship; it’s a cohabitation. You’re domestic partners and you have to select wisely. So, you need to find a partner who can help you make a smooth transition to your desired level of cloud adoption, since you’re going to be there a very long time.
This post was written as part of the IBM for Midsize Business program, which provides midsize businesses with the tools, expertise and solutions they need to become engines of a smarter planet.










You must be logged in to post a comment.